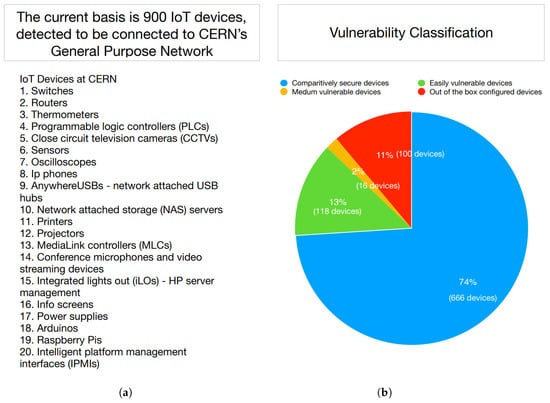
Sensors | Free Full-Text | Detecting IoT Devices and How They Put Large Heterogeneous Networks at Security Risk
Strategies to End Commercial Sexual Exploitation of Youth: A toolkit for collaborative action | National Center for Youth Law

TheHackerGiraffe & PewDiePie Printer Predicament Using The Printer Exploitation Toolkit PRET - YouTube











![How to Hack and Exploit Printers in Seconds - HackingPassion.com : root@HackingPassion.com-[~] How to Hack and Exploit Printers in Seconds - HackingPassion.com : root@HackingPassion.com-[~]](https://hackingpassion.com/how-to-hack-and-exploit-printers-in-seconds/featured-image.png)